Ask About Cloud Syncing Options 3466136036

Cloud syncing is a critical component for modern data management. It allows users to store and access files across multiple devices seamlessly. Various services offer unique features such as file versioning and security measures like end-to-end encryption. Evaluating these options requires understanding specific needs including storage limits and synchronization frequency. Engaging with experts can provide clarity. However, the decision-making process may be more complex than anticipated, raising further questions about the best approach.
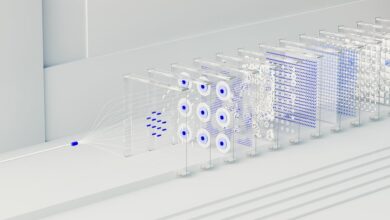
Understanding Cloud Syncing: What It Is and How It Works
Cloud syncing refers to the process of storing and synchronizing data across multiple devices via internet-connected cloud storage solutions.
This mechanism leverages cloud technology to enhance data accessibility, allowing users to access files anytime, anywhere.
Key Features to Look for in Cloud Syncing Services
When evaluating cloud syncing services, several key features become paramount for users aiming to optimize their data management.
Essential criteria include:
- File Versioning: Ensures recovery of previous document iterations.
- Sync Frequency: Determines how often files are updated.
- Cross-Platform Compatibility: Supports diverse devices for seamless access.
- End-to-End Encryption: Safeguards data integrity during transfer.
These features collectively enhance user experience and data security.
Popular Cloud Syncing Options Available Today
In the rapidly evolving landscape of data management, numerous cloud syncing options have emerged, each catering to diverse user needs and preferences.
Popular services such as Google Drive, Dropbox, and Microsoft OneDrive offer robust file synchronization capabilities, ensuring seamless access across devices.
These platforms excel in cross platform compatibility, enabling users to maintain productivity regardless of their operating system or device type, thereby enhancing data accessibility.
Security Considerations for Cloud Syncing
As users increasingly rely on cloud syncing services for data management, the importance of security measures cannot be overlooked.
Key considerations include:
- Implementation of robust encryption protocols to safeguard data in transit and at rest
- Regular audits to ensure compliance with data privacy regulations
- Multi-factor authentication to enhance user access security
- User education on recognizing phishing attempts and securing personal information
These measures collectively bolster data integrity.
Choosing the Right Cloud Syncing Solution for Your Needs
How can users effectively navigate the myriad of cloud syncing solutions available today?
By evaluating syncing strategies tailored to their unique needs, individuals can enhance data accessibility while ensuring optimal performance. Factors such as storage capacity, synchronization speed, and cross-platform compatibility should be analyzed.
Ultimately, selecting the right solution empowers users, providing them with the flexibility to manage their data effectively and securely.
Conclusion
In the realm of cloud syncing, choosing the right service is akin to selecting the ideal tool for a craftsman. Just as a master carpenter meticulously chooses between a chisel and a saw to shape wood, users must assess their unique needs—be it storage capacity or security features—to ensure their data is sculpted seamlessly. By evaluating options and engaging with knowledgeable representatives, individuals can forge a robust digital workspace, ensuring their information flows as smoothly as a well-crafted masterpiece.