Velocity Arc Start 336-218-3920 Fueling Verified Caller Lookup

Verified caller lookup combines sender data with trusted databases to produce auditable, labeled alerts. The approach enhances connect rates and recipient trust while preserving privacy. Fuel-efficient routing optimizes verification paths without sacrificing speed or accuracy. Safeguards and compliance frameworks ensure independent audits and clear consent. This balance between verification rigor and efficiency invites further examination of implementation details, governance, and practical outcomes as the method scales.
What Is Verified Caller Lookup and Why It Matters
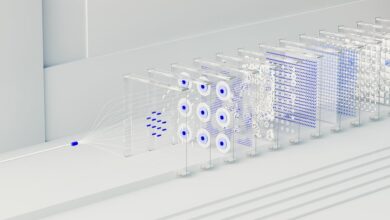
Verified Caller Lookup is a system that confirms the identity of a caller by cross-referencing sender information with trusted databases and telephony signals. It clarifies how digital traces support outreach, reducing uncertainty. What is verified becomes observable through verified alerts and validated metadata. Caller lookup provides transparency, enabling informed decisions while preserving user autonomy and safeguarding privacy.
How Verified Numbers Improve Connect Rates and Trust
Verified numbers can significantly raise connect rates by assuring recipients of legitimate intent, which reduces call reluctance and misdials. In practice, verified numbers foster verified trust, signaling credibility and reducing friction in outreach. This clarity enhances caller routing efficiency, ensuring each contact lands with the intended recipient. The approach supports freedom-oriented strategies by aligning trust with direct, purpose-driven communication.
Implementing Fuel-Efficient Routing for Verifications
Implementing fuel-efficient routing for verifications focuses on directing verification calls through paths that minimize energy use without compromising accuracy or speed. The approach emphasizes measured routing choices, leveraging verified calling practices to reduce redundant hops and idle time. Outcomes include lower operational footprints, improved response consistency, and transparent logging for a security audit, while maintaining verification integrity and user autonomy.
Safeguards, Compliance, and Best Practices for 2026
Safeguards, compliance, and best practices for 2026 establish a framework to ensure verification processes remain secure, auditable, and user-respecting as technologies evolve.
The approach emphasizes transparency, accountability, and continual assessment of what-ifs and risk mactors.
It advocates modular controls, independent audits, and clear user consent, balancing innovation with privacy, resilience, and lawful access, while sustaining public trust and operational integrity.
Conclusion
In the end, Velocity Arc Playbook proves that verified caller lookup isn’t magic—just well-behaved data pretending to be a clairvoyant, with auditable breadcrumbs for every misdial. The satire writes itself: trust, transparency, and fuel-efficient routing walk into a conference call and emerge slightly more credible than a caller ID pun. Stakeholders praise resilience, privacy, and consent, while investors pretend they understand the telephony jargon. The verdict: efficiency with accountability, served with a wink.