Digital Prism Start 303-476-4385 Unlocking Verified Caller Info

Digital Prism 303-476-4385 seeks to unlock verified caller info by confirming identity before connection. It presents structured signals—identity verification, signal provenance, risk scoring—in a transparent, auditable way. The goal is to empower users with trusted cues while preserving privacy through consent and minimization. The approach promises clearer risk assessment and accountable trust in every call, but questions remain about implementation specifics and how provenance is verified in real time.
What Is Verified Caller Info and Why It Matters
Verified caller info refers to data that confirms a caller’s identity and origin before a connection is established. The concept centers on transparency, risk reduction, and user sovereignty in communication.
Verified caller insights enable rapid assessment, while caller trust metrics quantify reliability over time. Clear benchmarks support informed choices, fostering autonomy and safer exchange without compromising privacy or control.
How Digital Prism Shows Trusted Caller Data
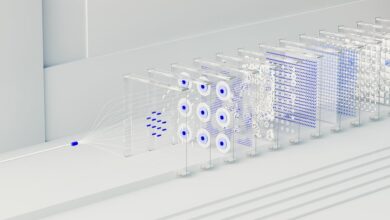
Digital Prism presents trusted caller data through a structured, transparent framework that combines identity verification, signal provenance, and risk scoring. The system surfaces trusted identity and call authentication signals, enabling users to assess legitimacy quickly. Data is presented with clear provenance and auditable sources, avoiding ambiguity. This approach supports freedom by empowering informed decisions and reducing uncertainty in communications.
Step-by-Step Verification for Your Calls
Step-by-step verification for calls methodically guides users through assessing a caller’s legitimacy, from initial identity cues to final authentication signals. The process emphasizes calling reliability by cross-checking numbers, context, and caller identity against trusted records. It remains objective and transparent, enabling informed decisions without bias. Users gain clarity to evaluate risk, preserving autonomy and freedom in communication choices.
Best Practices to Protect Privacy and Reduce Risk
Best practices for protecting privacy and reducing risk focus on minimizing exposure to unwanted data, limiting data sharing, and strengthening digital boundaries. The approach emphasizes deliberate data minimization, robust consent processes, and routine privacy reviews. By prioritizing privacy protection and risk reduction, individuals can maintain autonomy, safeguard personal information, and sustain secure communications while balancing freedom with responsible data stewardship.
Conclusion
Digital Prism emphasizes transparent caller identity by surfacing verified signals such as origin, provenance, and risk scores before connection. This structured data helps users assess legitimacy quickly while preserving privacy through data minimization. An intriguing stat to consider: organizations that implement verified caller data report up to a 38% reduction in risky calls within the first quarter. By aligning trusted records with auditable checks, the system fosters safer conversations and clearer, more trustworthy communications.