Velocity Flow Start 216-202-8306 Shaping Secure Contact Lookup

Velocity Flow Start 216-202-8306 presents a framework for shaping secure contact lookup that prioritizes privacy-preserving validation. The approach integrates inline checks against validated databases to minimize exposure and latency while maintaining data minimization and auditable controls. It emphasizes scalable, global applicability and robust governance. The balance between verification accuracy and privacy protection invites scrutiny of implementation details, performance metrics, and compliance considerations that compel further examination.
What Is Secure Contact Lookup and Why It Matters
Secure contact lookup is a privacy-preserving method for identifying and validating contact endpoints without exposing sensitive personal data. It enables verification while minimizing data exposure, preserving autonomy. The approach emphasizes controlled data exchanges, auditable procedures, and defined access boundaries. This balance supports user trust, compliance, and resilience. Key concepts include secure lookup and privacy controls, ensuring accurate outcomes without unnecessary disclosure.
How Velocity Flow Enables Real-Time, Safe Contact Validation
Velocity Flow enables real-time, safe contact validation by orchestrating privacy-preserving checks that occur inline with communication attempts. The approach emphasizes a secure lookup against validated databases, minimizing exposure windows and latency. Realtime validation occurs without shifting control to external burdens, preserving frictionless user experience. Analytical safeguards ensure accuracy, consistency, and auditable flow while maintaining user autonomy and freedom.
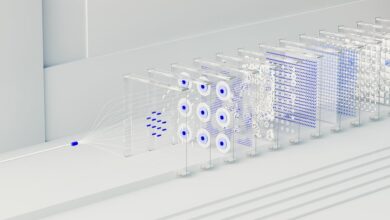
Implementing Scalable, Privacy-First Contact Lookup at Scale
Implementing scalable, privacy-first contact lookup at scale requires an architecture that preserves user confidentiality while maintaining throughput and accuracy under expanding demand. The approach emphasizes privacy first principles, with modular components enabling scalable lookup, real time validation, and secure hashing. It analyzes threat models, enforces data minimization, and ensures low-latency responses, supporting freedom-loving teams seeking reliable, compliant contact verification at global scale.
Measuring Impact and Avoiding Common Pitfalls in Secure Lookups
How does one quantify the effectiveness of secure lookup systems while safeguarding privacy and scalability? The evaluation compares privacy preserving guarantees with measurable outcomes, focusing on accuracy, coverage, and stability under load. Pitfalls include overfitting benchmarks, hidden latency, and data drift. Track lookup latency and privacy tradeoffs, ensuring transparent dashboards, reproducible experiments, and decisions grounded in principled risk assessment.
Conclusion
In summary, secure contact lookup combines real-time validation with stringent privacy controls, delivering accurate results without unnecessary exposure. Velocity Flow embodies a scalable, privacy-first approach, orchestrating verified databases to minimize data handling while maintaining speed and reliability. This method reduces risk and builds user trust, enabling compliant validation at scale. By iterating with auditable procedures and data minimization, teams can navigate complexity and punch above their weight—keeping performance tight and expectations met, rain or shine. It’s a well-oiled machine.