Velocity Arc Start 325.38.10.46.791 Shaping IP Lookup Insights

The discussion centers on how IP lookup informs shaping decisions within the velocity arc framework. It employs quantitative metrics, event signals, and timing patterns to reveal routing behavior, latency, and packet loss. The goal is to map stable regimes to perturbations and identify causality and lag. Analysts must define objectives, instrument data, and calibrate models to produce repeatable, auditable outcomes. This framing leaves a gap that invites further inquiry into practical implementation and validation.
How IP Lookup Shaping Drives Network Decisions
IP lookup shaping informs network decisions by evaluating how latency, routing stability, and packet loss influence the throughput and quality of service across paths.
The approach analyzes IP telemetry, shaping routing signals and client experience.
Data enrichment supports anomaly detection, revealing deviations from expected routes.
Conclusions guide policy adjustments, aligning infrastructure with performance goals while preserving freedom to adapt to changing conditions.
Decoding Velocity Arc: Metrics, Signals, and Patterns
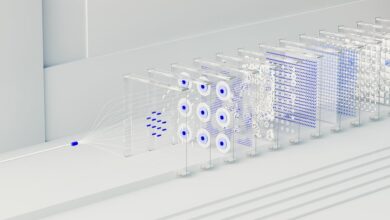
The Velocity Arc integrates quantitative metrics, event signals, and temporal patterns to reveal how traffic flows evolve across networks. It dissects velocity arc data into discrete components, aligning metrics signals with time windows to identify causality and sequence. Analysts assess correlation, lag, and anomaly indicators, mapping stable regimes against perturbations, ensuring clarity in interpretation while preserving freedom of inquiry and methodological rigor.
Practical Guides to Implementing IP Lookup Insights
Are practical challenges in IP lookup insights best addressed through a structured, stepwise approach that anchors data quality to actionable outcomes? Implementers adopt a disciplined workflow: define objectives, instrument data collection, apply fault detection to cleanse inputs, calibrate lookup models, and validate results. Traffic normalization ensures comparability across sources, enabling repeatable decisions and measurable improvements in operational transparency and reliability.
From Latency to Security: Use Cases and Operator Takeaways
From latency data to security implications, the section outlines concrete use cases that demonstrate how timing measurements can inform threat detection, anomaly attribution, and policy enforcement.
Data latency informs threat modeling by quantifying delays across paths, enabling operators to separate benign variance from malicious activity, and to calibrate alert thresholds without overreacting.
Clear, repeatable workflows support disciplined decision-making and resilient defenses.
Conclusion
IP lookup shaping translates telemetry into disciplined routing decisions, aligning metrics, signals, and temporal patterns to reveal causality and resilience gaps. By calibrating data collection, models, and validation, operators establish repeatable workflows that optimize throughput while maintaining security postures. Example: a regional ISP detects sporadic latency spikes via time-window analysis, traces them to a misbehaving edge cache, and reconfigures shaping rules to preserve intercity performance without sacrificing reliability. This methodical approach fosters predictable, defensible network behavior.