Stellar Gateway Start 215-478-8344 Inspiring Caller Identification Paths

Stellar Gateway Start 215-478-8344 proposes a framework for Inspiring Caller Identification Paths that blends authentication standards with transparent provenance. The approach emphasizes verifiable signals, modular governance, and auditable workflows to curb spoofing. It prioritizes human-centered prompts and accessibility to reduce cognitive load while preserving precision. The resulting design invites scrutiny of source lineage and consent, inviting stakeholders to weigh trade-offs and future refinements as technology and policy evolve.
What Is Inspiring Caller Identification and Why It Matters
Inspiring caller identification refers to the deliberate design and use of caller IDs to shape recipient perception, trust, and engagement in telecommunication interactions.
This analysis evaluates mechanisms that influence user interpretation, delineates operational boundaries, and measures impact on behavior.
It examines how data accuracy, signaling integrity, and policy controls drive inspiring trust while maintaining ethical transparency within configurable communication ecosystems.
How Authentic Sources Build Trust in Caller IDs
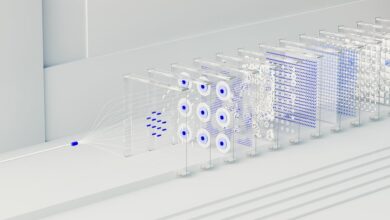
Authenticity in caller IDs hinges on credible sourcing, rigorous verification, and standardized signaling that collectively deter spoofing and manipulation. The analysis identifies institutional chains of evidence, independent audits, and cross-reference protocols as core mechanisms. Ethical verification reinforces legitimacy while Brand transparency clarifies lineage and purpose. Trust emerges when verifiers publish criteria, and carriers enforce consistent authentication across networks, enhancing user confidence and system resilience.
Designing Human-Centered Prompts for Clear Identification
Designing human-centered prompts for clear identification involves structuring prompt logic to elicit precise, unambiguous responses from users while respecting cognitive load and accessibility. The approach evaluates Trustworthy Protocols and Empathy Signals, balancing determinism with user autonomy. It emphasizes minimal ambiguity, explicit intent, and consistent terminology, enabling scalable verification. This analytical framework supports transparent interactions, fostering freedom through accountable, user-centric design principles.
Practical Steps to Implement Inspiring Caller Identification Paths
From the prior discussion on human-centered prompts, the practical path to implementing Inspiring Caller Identification Paths centers on translating identified principles into concrete workflows, tooling, and governance. The approach emphasizes Understanding Your Audience and Ethical Data Use, aligning data collection, labeling, and consent with transparent policies. Technical steps include modular pipelines, audit trails, and governance reviews for accountable, freedom-respecting deployment.
Conclusion
In sum, inspiring caller identification hinges on authentic signaling, transparent provenance, and modular governance that together reduce spoofing and boost user trust. By embedding verifiable sources, auditable workflows, and human-centered prompts, systems achieve clearer, more actionable identification while honoring consent and accessibility. Anachronistically, like a Renaissance guild issuing immutable seals for each message, this approach insists on traceable lineage and independent audits, ensuring accountable paths that align technical rigor with audience needs and institutional integrity.