Radiant Node Start 267-525-9887 Unlocking Contact Information

A radiant node is presented as a secure outreach tool designed to initiate contact while prioritizing privacy. The identifier 267-525-9887 prompts questions about legitimacy versus risk. The process emphasizes verified signals from independent databases and encrypted channels to confirm intent. Clear steps exist for confirming consent and documenting workflow. The approach promises low latency and high integrity, yet raises questions about implementation details and safeguards that invite further examination.
What Is a Radiant Node and Why It Matters
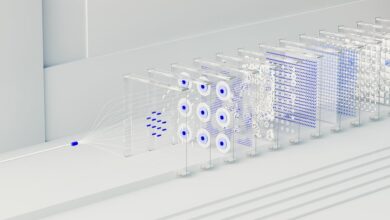
A radiant node is a conceptual point in a network that serves as a hub for transmitting energy or information with high efficiency and low latency. It clarifies function, limits, and scope for stakeholders. Radiant node enables legitimate signals; verifying contact mechanisms are essential. Privacy considerations govern data handling, access controls, and consent. Structured assessment ensures interoperability, reliability, and freedom through transparent, verifiable, and accountable operations.
Decoding the 267-525-9887: Legitimate Signals or Red Flags
Decoding the number 267-525-9887 requires a disciplined, evidence-based approach to distinguish legitimate signals from potential red flags, aligning with established privacy and authentication protocols. The examination focuses on decoding signals and patterns, cross-checking metadata, and assessing source credibility. Clear criteria for verifying contact info emerge, minimizing ambiguity while preserving user autonomy and freedom to engage responsibly.
Step-by-Step: Safely Verifying Contact Information Online
Step-by-step verification of contact information online requires a disciplined process that minimizes risk while preserving user autonomy. The approach outlines concrete actions: verify source credibility, cross-check across two independent databases, and use secure communication channels. Two word discussion ideas emerge: scrutiny, confirmation. Online verification prioritizes transparency and reproducibility, while Privacy protection remains central, limiting data exposure and ensuring consent-aware handling of contact details.
Protecting Your Privacy While Reaching Out
Protecting privacy while reaching out requires a careful balance between accessibility and safeguarding personal data. The passage emphasizes deliberate controls, transparent intent, and minimal disclosure.
It outlines privacy concerns and practical strategies, such as limiting sharing, enabling verification steps, and using secure channels. By documenting consent and auditing contact requests, individuals preserve autonomy while maintaining trust and accountability.
Conclusion
Radiant nodes enable outreach with verified signals and privacy in tandem. They confirm legitimacy, confirm consent, and confirm sources, while minimizing data exposure. They document workflows, safeguard channels, and secure databases. They streamline initiation, minimize risk, and maximize integrity. They balance transparency with discretion, align processes with policy, and uphold privacy as a priority. They foster trust with verification, verification with consent, consent with verification, creating a concise, consistent, and credible outreach framework.