Radiant Node Start 303-242-3255 Driving Caller Data Search

Radiant Node initiates a structured caller data search by converting dial-tone signals into traceable source attribution. The approach emphasizes reproducibility, governance, and cross-system logging to create auditable contact histories. Enrichment is balanced with privacy checks and compliance steps, ensuring accountability from signal receipt to archival record. The workflow highlights practical workflows, rapid troubleshooting, and risk-aware decision points, but leaves unresolved how specific data fusion choices impact provenance and outreach outcomes. Further exploration is warranted.
How Caller Data Searches Work: Foundations and Goals
Caller data searches are structured processes that aim to locate relevant information about a caller by querying multiple data sources and applying consistent matching criteria. The approach emphasizes reproducibility, traceable methods, and objective metrics. Foundations include data standards and governance, while goals focus on accuracy, minimal false positives, and efficiency. Privacy considerations and transparent procedures guide decision-making and risk assessment.
Validate and Trace Numbers: From Dial Tone to Source
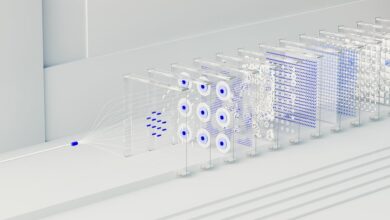
Validate and trace numbers entails a disciplined, data-driven sequence that converts dial-tone signals into accountable source attribution. The analysis proceeds through controlled logging, standardized identifiers, and cross-system verification to ensure traceability. Call tracing emerges as a structured process, not a singular event, while data provenance underpins integrity from initial signal to archival record. This approach preserves freedom through transparent, reproducible handling.
Build Precise Contact Histories: Enrichment, Privacy, and Compliance
This topic examines the systematic construction of precise contact histories by integrating enrichment, privacy considerations, and compliance requirements into a unified data workflow. The analysis remains analytical, methodical, and empirical, presenting structured steps for data fusion, provenance, and auditability. It highlights contact enrichment techniques and aligns processes with privacy compliance mandates, ensuring traceable, auditable, and responsible caller data management.
Practical Workflows and Troubleshooting for Real‑World Outreach
Practical workflows for real-world outreach demand a disciplined approach to process design, execution, and rapid troubleshooting within dynamic environments. The analysis emphasizes systematic caller matching, data enrichment, and privacy compliance as core checks. Empirical evaluation guides outreach workflows, flags interference risks, and informs corrective actions. This detached view favors measurable outcomes, repeatable steps, and minimal ambiguity for freedom‑seeking practitioners.
Conclusion
In sum, the Radiant Node workflow converts dial-tone signals into auditable contact histories through disciplined data fusion, enrichment, and privacy checks. Each step is traceable, repeatable, and governed, enabling rapid troubleshooting and risk-aware decision making. The system acts like a well‑orchestrated engine, where inputs become accountable outputs only after passing through validation, provenance, and compliance gates. This disciplined cadence yields reliable outreach outcomes while preserving privacy and governance as core constants.