Infinite Arc Start 267-838-9030 Unlocking Reliable Contact Data
Infinite Arc starts with a disciplined view of contact data. It treats data provenance, validation, and reconciliation as core signals. The approach maps sources, audits latency, and tests failover to reveal strengths and gaps. Metrics are collected to prove reliability, not just claim it. The framework invites scrutiny and ongoing improvement. A careful reader will see how governance and hygiene become practical assets, prompting further inquiry into how these practices shape trust and outcomes.
What Makes Contact Data Reliable and Why It Matters
Reliable contact data hinges on accuracy, completeness, and timeliness, all of which directly influence measurement, targeting, and outreach outcomes. The investigation identifies how reliable data underpins confidence, minimizes risk, and sustains autonomy. In this framework, contact data acts as a verifiable asset—material for decisions, not conjecture. Gaps erode trust; rigor ensures usable, freedom-affirming insights.
How to Assess Data Quality Across Sources
Assessing data quality across sources requires a structured, evidence-based approach that surfaces both strengths and gaps. The investigation examines data provenance to trace origins, lineage, and transformations, revealing reliability and biases. Validation metrics quantify accuracy, completeness, and consistency, enabling cross-source reconciliation. Findings emphasize reproducibility and auditability, guiding decisions about source trust, integration viability, and governance, while preserving freedom to act on verified insights.
Practical Steps to Build a Resilient Data Pipeline
A practical data pipeline demands a disciplined, evidence-based approach to stability and continuity, iterating from ingestion to delivery with explicit guardrails and measurable outcomes.
The investigation traces data lineage, monitors latency, and enforces retries, ensuring reliable pipelines through modular design and failover tests.
Clear ownership and data stewardship enable proactive anomaly detection, while freedom-loving teams pursue continuous improvement and auditable resilience.
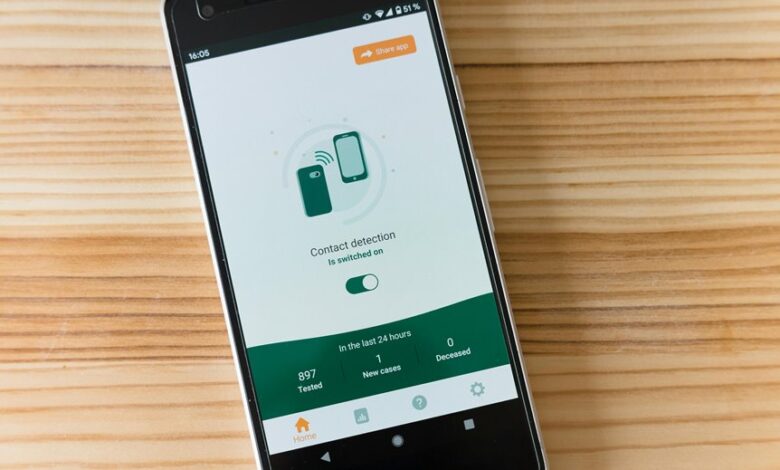
Best Practices for Compliance, Deliverability, and Hygiene
To ensure compliant, deliverable, and hygiene-conscious data operations, organizations should map regulatory requirements, quantify risk, and implement traceable controls across ingestion, processing, and distribution. Investigators evaluate data normalization procedures, consent tracking methods, and audit trails to measure exposure, enforce policy, and sustain trust. Deliberate, data-driven scrutiny reveals gaps, enabling freedom-loving teams to implement precise, verifiable hygiene practices without compromise.
Conclusion
This investigation reveals that reliable contact data, while elusive, becomes approachable through disciplined provenance and quiet vigilance. By tracing sources, validating metrics, and rehearsing failovers, teams inch toward resilience without fuss. Privacy and consent are not barriers but checkpoints, guiding ethical expansion. In the end, a calm, data-driven cadence—monitored latency, auditable trails, and modular pipelines—delivers trustworthy leads, enabling growth with understated confidence and verifiable accountability.