Infinite Arc Start 248-939-8217 Fueling Verified Caller Search

Infinite Arc Start 248-939-8217 frames a system for Verified Caller Search by tying accuracy to expanding reach. It emphasizes disciplined measurement, governance, and privacy-preserving data provenance. The approach seeks auditable quality controls and consent-driven data use, aiming to sustain trust as scope grows. The question remains how scalable safeguards and transparent decision points will hold up under practical deployment, inviting closer scrutiny of data sources, verification methods, and user expectations.
What Is Verified Caller Search and Why It Matters
Verified Caller Search refers to a verification process that confirms the identity and legitimacy of a caller, typically by cross-referencing provided details with trusted data sources. The method centers on transparency, reliability, and consent. It reduces risk, fosters trust, and enables informed decisions. For stakeholders, verified caller information enhances security, accountability, and efficiency within the caller search ecosystem.
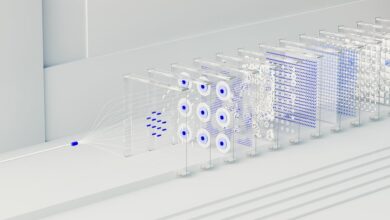
The Infinite Arc Concept: Mapping Accuracy to Scale
The Infinite Arc Concept maps how accuracy scales with system reach, illustrating how precise signals maintain reliability as scope expands. It presents a disciplined view of measurement, clarity, and boundaries, emphasizing structured evaluation over guesswork.
infinite arc, mapping accuracy; verified caller, search relevance. The narrative remains detached, technical, and accessible, supporting freedom through transparent, scalable verification without compromising privacy or intent.
Building a Trusted Lookup: Data, Verification, and Privacy
Building a trusted lookup requires a structured approach to data quality, verification processes, and privacy safeguards. A robust trust framework anchors governance, consent, and accountability. Data provenance clarifies origins, lineage, and changes, ensuring traceability. Clear, auditable checks mitigate bias and errors while preserving user autonomy. Transparent handling promotes freedom, security, and confidence in verification without compromising privacy or integrity.
Practical Roadmap to Implement Verified Caller Search Today
How can organizations implement a practical, ready-to-deploy verified caller search system today? A practical roadmap emphasizes governance, architecture, and phased deployment. Core components include trusted data sources, continuous verification, and robust privacy controls. Emphasize automation to improve lookup accuracy, scalable APIs, and clear SLAs. Maintain transparency with users, monitor performance, and iterate to sustain secure, freedom-centric verification of verified caller identities.
Conclusion
In the hush of a data-driven dawn, the Infinite Arc unfurls like a widening dawn sky. Each verified cue glimmers—a beacon threaded through networks, a lighthouse guiding trust toward crowded harbors. As scale grows, safeguards tighten, and provenance stays visible, crisp as frost on glass. The arc hums with disciplined governance, transparent intent, and user consent, turning raw signals into reliable guidance. The imagined horizon becomes a practical roadmap, inviting steady, responsible expansion toward trusted caller identification.